How to secure your WordPress site!
First published November 2014. Updated November 2016, December 2017, October 2018, December 2020.
Taking preemptive action to prevent security breaches to your website is a wise business decision. Here are some of the steps you can take to secure your WordPress website.
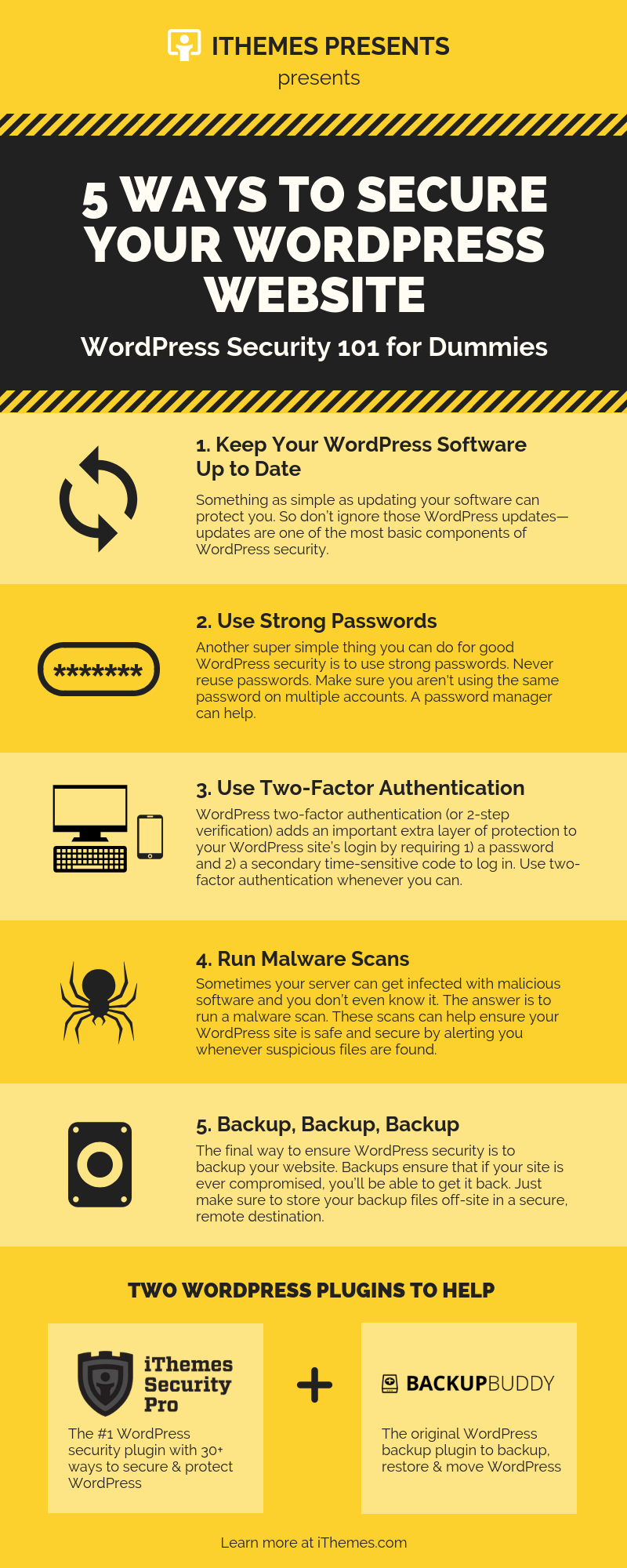
- Install and configure a security plugin. We use iThemes Security Pro.
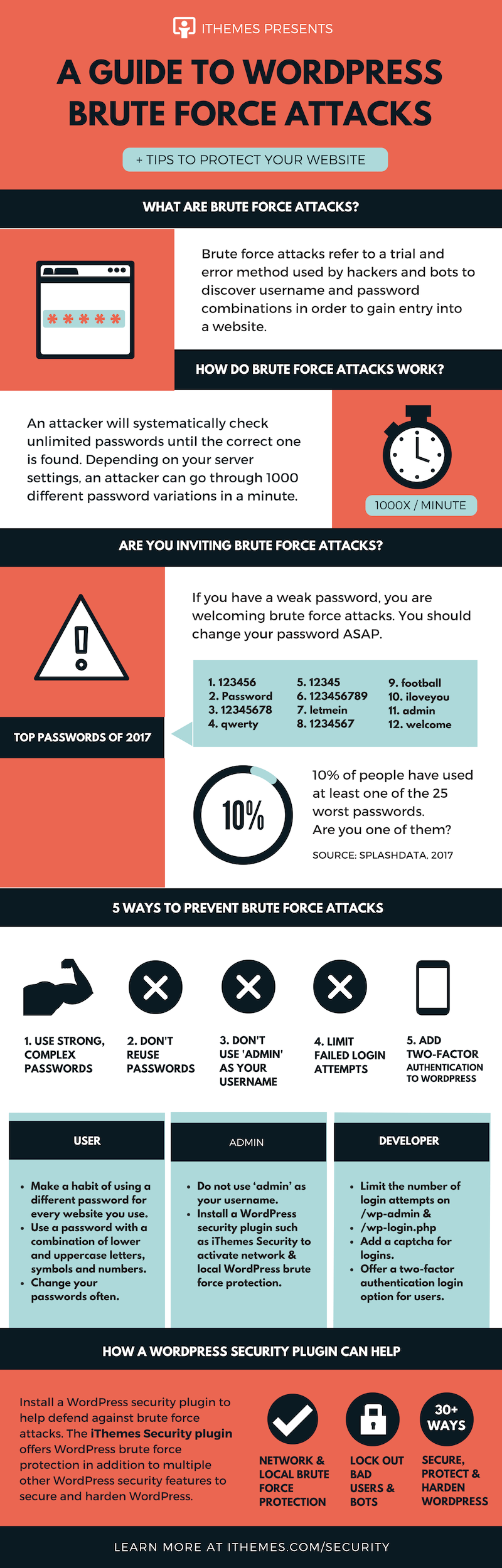
- Activate Two Step Authentication, also known as Two-Factor Authentication, an excellent method of preventing unauthorized access.
- Schedule a daily automated database backup such as Backup Buddy.
- Install the Akismet comment spam detector plugin, obtain and insert your API code.
- Insert WordPress Salt keys in the wp-config.php file and change them regularly using the Salt Shaker plugin: More information
- Update WordPress to the latest version: More information WordPress releases new versions regularly. You should always be using the latest release.
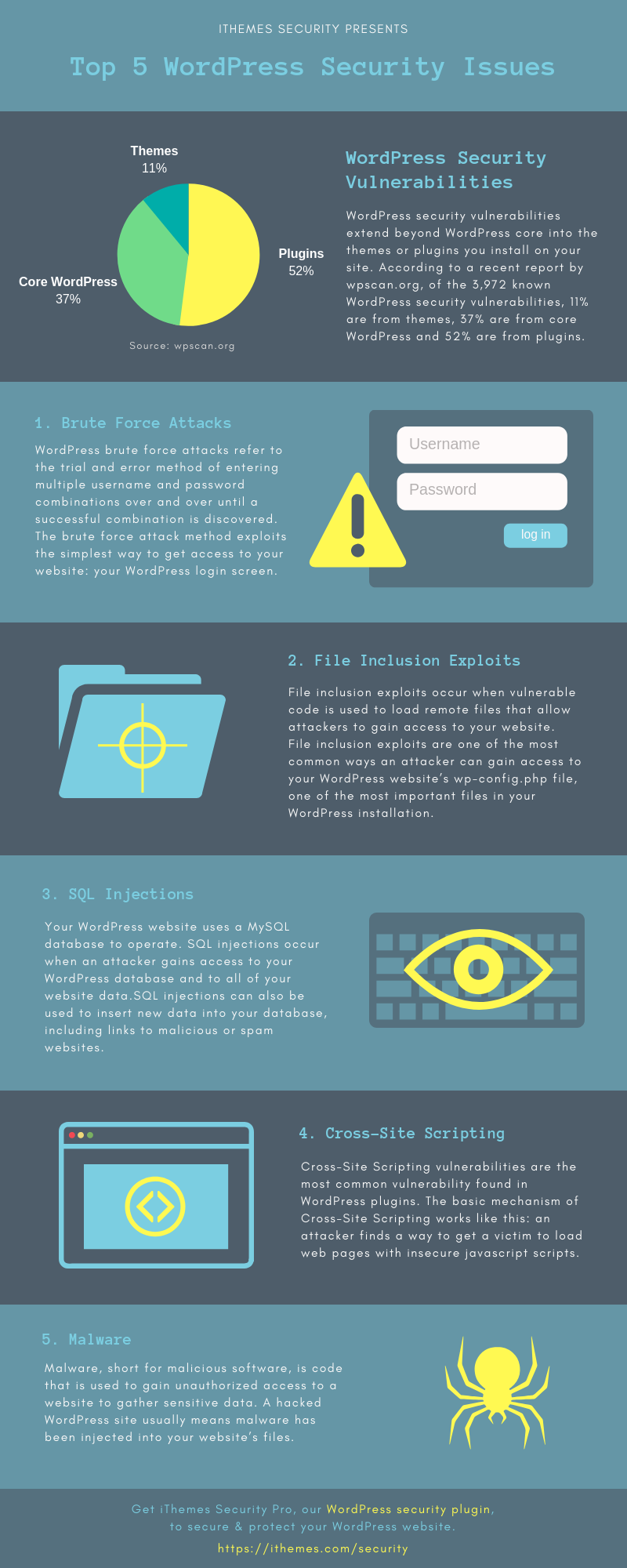
- Update all plugins to the latest versions More information, This is very important for security and functionality.
- Upgrade your WordPress Theme to the latest version. All modifications to your theme should be made in a child theme, allowing you to always use the latest version of the ‘parent’ theme.
- Monitor your site to be notified if the site is ‘down’. We use iThemes Sync.
- Backup all WordPress, plugin and theme files to an external location: More Information
- Scan the site for malware to ensure the site is safe: More information
- Check your Google Search Console for errors.
- Remove unused plugins and themes that may have security vulnerabilities
- Create and use only strong passwords! Please also see: How to Set Up a Strong Password
- Ensure that all passwords are strong: More Information
- Check the PHP Error Log and repair any errors: More information
- Ask you host to update you to the latest version of PHP. More Information.
- Ensure the domain registrar has the correct Whois registration data: More information
- Empty comment spam: More information
- Install and configure WP Optimize. Schedule regular database repair and optimization: More information
- Review File Permissions.
- Check the Secunia Advisory and Vulnerability Database for plugin security vulnerabilities: More Information
- Obtain an SSL encryption certificate. These are not expensive, we include them in our hosting package, and are a Google ranking factor.